United States Courts virus is a scam. This kind of scam has been going on for around a year under other names all across the world. The makers use the name of a government agency or authority or some kind and attempt to scare users into paying a false fine.
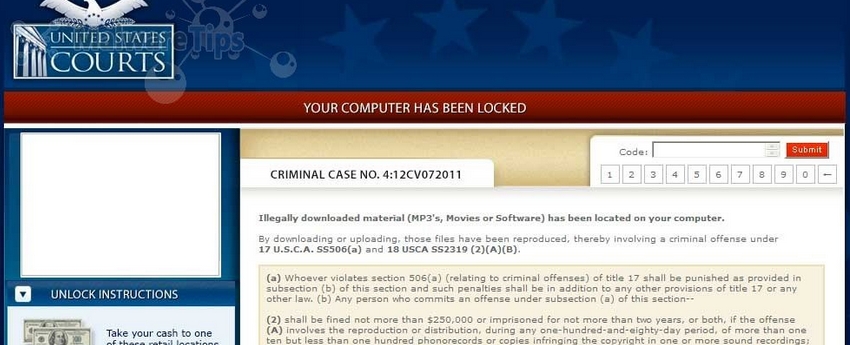
Past scams just like this in the U.S. are the FBI Money Pak, The US Treasury, Immigration and Customs. Basically anything that looks official.
Manual Removal of United States Courts virus is possible but not recommended.
What Damage Is Being Done by United States Courts virus?
This virus can do damage to the core operating system. It will often times block the use of your computer until you pay the FAKE fine. We can’t stress enough that the warnings given off from this virus are BOGUS and NOT real. Do not pay the fake fine.
The virus will capture the users IP address and accuse the person who is using this IP of pirating software and the like. It will turn the web cam on if one is installed and snap a picture of the user. This is done as a scare tactic to really make the user think it’s an official fine.
Automatic Virus Removal
 SpyHunter is very user friendly, providing you with a simple interface that will allow you to properly understand the options and functions available. SpyHunter succeeds at both cleaning your already infected computer from viruses and to prevent virus infections in the future. Simply put IT WORKS!
SpyHunter is very user friendly, providing you with a simple interface that will allow you to properly understand the options and functions available. SpyHunter succeeds at both cleaning your already infected computer from viruses and to prevent virus infections in the future. Simply put IT WORKS!
Online Virus Removal Service
 Do you need Expert Help! PCNinja.com has experts standing by that can fully remove this virus from your computer. Based in the U.S.all repairs are down by certified computer repair experts. They have fixed thousands of computers over the years and RemoveVirus.org is proud to recommend this U.S. based company to service your computer. Visit http://www.pcninja.com or call 1-888-392-2785
Do you need Expert Help! PCNinja.com has experts standing by that can fully remove this virus from your computer. Based in the U.S.all repairs are down by certified computer repair experts. They have fixed thousands of computers over the years and RemoveVirus.org is proud to recommend this U.S. based company to service your computer. Visit http://www.pcninja.com or call 1-888-392-2785
8am-10pm PST
United States Courts virus Manual Removal Procedures
Manual removal is not recommended for normal computer users.
This threat can be very hard to remove manually. We will need to at the very least download a AV scanner to locate the virus traces.
- [random].exec ( Example is 6KJF55K4.EXE ) Your file trace will be named different.
Some Tips on Locating the file.
Known File Paths. To view these file paths you will need to either manually type them in or show hidden files and folders. Learn how to at
- C:\Documents and Settings\USER NAME\Local Settings\Application Data
Windows Vista/ Windows 7/ Windows 8:
- C:\ProgramData\
- C:\Users\Your User Name\AppData\
- C:\Users\Your User Name\AppData\local
- C:\Users\Your User Name\AppData\Roaming
A. To find the file name we recommend you run a free scan using SpyHunter. The free scan will show you the exact file name and full path of the executable that you need to delete. This is the easiest way to locate it.
B. Browse to the file location shown above. Sort the files by date and see if any of the file names match the date you where infected. Only a few files should be around the same date of the infection. From there you can re-name the file you believe is the virus and restart your computer. Once you have re-booted you can now delete that file.
While you may not know the exact name of the file here are a few tips to locate it.
C: Log-into another users account and see if you can delete the file. Again use the File Locations below to locate the file
D: Start the Task Manager the very second you login and terminate the process that way.
Once you have been able to remove the main executable your computer will run as normal. If you have not purchased an anti virus client for your computer you should consider doing so. This will prevent you from being infected again. If you need advanced help we do recommend PCNinja.com or you can always just ask your questions below.

its actually simple to remove..been doing computers for over 30yrs.honestly dont add to much bloat/removal software if you dont have to..there are some free ones that knock it right out.you only need(one)virus protection program and one (manual malware)protection..no more…..otherwise they fight each other.