The transition from DDR to DDR2 memory was more evolutionary than revolutionary, the DDR2 architecture being essentially the same as that of its predecessor, with a number of enhancements designed to provide greater bandwidth and other features that help reduce power consumption:
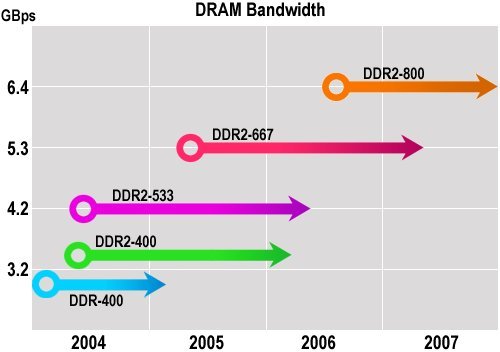
- Higher memory transfer rates: DDR2 supports higher-speed transfer rates than DDR, which is officially found in 266 megatransfers per second (MTps), 333 MTps, and 400 MTps versions. Current DDR2 industry specifications call for 400 MTps, 533 MTps, 667 MTps and 800 MTps.
- 4n prefetch: DDR2 devices use a 4n prefetch architecture instead of the 2n prefetch used for DDR. Using DDR2, the internal DRAM core is designed to read or write data at four times the width of the device’s external interface. In comparison, using DDR the internal DRAM core is designed to read or write data at twice the width of the device’s external interface. As a result, the internal DRAM core’s 4n prefetch architecture enables DDR2 to attain higher memory transfer rates than DDR.
- Reduced voltage: DDR2 devices use a supply voltage of 1.8 volts versus 2.5 volts for DDR – almost a 30 percent decrease in supply voltage. This voltage scaling enhancement has the potential to reduce overall power requirements for the memory subsystem.
DDR2 memories work with higher latencies than DDR memories, meaning that they delay more clock cycles to deliver a requested item of data. For this reason, the performance advantage of DDR2 over DDR was not fully seen in practice until the emergence of DDR2-533 versions, in mid-2004.
DDR2 is not backward compatible with DDR. Although DDR2 modules are the same length as DDR modules, differences exist in connectors, signalling, and supply voltages. For example, on DDR memories the resistive termination necessary for making the memory work is located on the motherboard, while on DDR2 memories this circuit is located inside the memory chip itself. Also, DDR modules have 184 contacts, while DDR2 modules have 240. Thus it is not possible to install DDR2 memories in DDR sockets or vice-versa.
The following table shows the bus frequency, data transfer rate, and bandwidth associated with each type of DDR2 module:
| DDR2 type | Module
speed grade |
Data
transfer rate |
Bandwidth
(per channel) |
|
|---|---|---|---|---|
| DDR2 at 400MHz | PC2-3200 | 200 MHz | 400 MTps | 3.2 GBps |
| DDR2 at 533 MHz | PC2-4300 | 266 MHz | 533 MTps | 4.3 GBps |
| DDR2 at 667 MHz | PC2-5300 | 333 MHz | 667 MTps | 5.3 GBps |
| DDR2 at 800 MHz | PC2-6400 | 400 MHz | 800 MTps | 6.4 GBps |
As processor power increased relentlessly – both by means of increased clock rates and wider FSBs – chipset manufacturers were quick to embrace the benefits of a dual-channel memory architecture as a solution to the growing bandwidth imbalance.
- What is Level 1 (L1) Cache Memory?
- What is L2 (Level 2) cache memory?
- RAM or Main Memory – PC / computer memory (DIMM, DRAM, SDRAM)
- DRAM – Dynamic Random Access Memory
- FPM DRAM
- EDO (Extended Data Out) and BEDO (Burst Extended Data Out) DRAM
- SDRAM
- PC133 SDRAM
- DDR SDRAM explained
- DDR2 DRAM
- Dual Channel DDR Memory
- 1T SRAM
- Direct DRAM
- SIMMs
- DIMM Memory
- RIMMs Memory
- Memory Presence Detection
- Parity Memory
- ECC Memory
- Memory Upgrades
- The Evolution of Memory
- Flash Memory
- Magnetic RAM