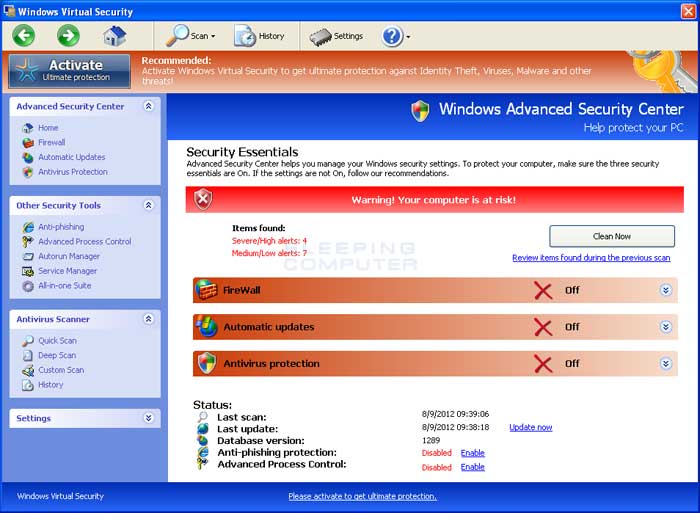
Windows Virtual Security
Welcome to another of our virus removal guides. This article will go over how to remove Windows Virtual Security. Infections of this type aren’t generally dangerous, but they can make using your computer unnecessarily difficult. Usually, infections of this type are simply designed to scare you into paying for them. They may also alter your browser’s search settings, making simple tasks, like finding this guide, head-splittingly difficult. This client is a clone of Anti-Spyware, XP Home Security 2012, XP Anti-Virus 2012 and XP Security 2012 as well as Win 7 Anti-Spyware, Win 7 Home Security 2012
How Did I get infected with Windows Virtual Security ?
Infections of this type come from webpages that have been exploited without knowledge of the website’s administrator. Frequently, you won’t even be asked to install anything, the infection will just show up on your computer without any interaction from you. If this is the case, you should consider upgrading to a different anti-virus.
How Much Damage is Windows Virtual Security Doing?
Most infections of this type don’t cause any lasting damage to your computer, aside from damaging the registry in very fixable ways. Usually, they remove the entry that tells Windows how to launch executable files. This is why you’re being asked what you would like to use to run every program that you try to launch the registry information that tells Windows how to run executables has been damaged. We’ve posted a quick fix for this below in the guide.
Windows Virtual Security
» Download
Windows Virtual Security Removal Software
How to Remove Windows Virtual Security ?
This article will cover the three major means to remove this infection:
1. Use Anti-virus software (Note you may need to follow the manual guide to start so you can install a client.)
2. Hire an expert ( We Recommend http://www.pcninja.com. This is a remote computer repair company)
3. Remove this threat yourself following our manual removal guide.
Automatic Windows Virtual Security Removal
Online Windows Virtual Security Removal Service
Windows Virtual Security Manual Removal Procedures
Step 1. If you are unable to run any executable programs at all this may be from the virus changing your registry settings. If this is the case you may need to use this patch. It is only for Windows 7 computers. Download Win 7 Fix exe Issue here.
Step 2. You need to stop and delete the main .exe file that is running Windows Virtual Security.
You should be able to locate this file at
- Protector-Random 3 to 4 characters .exe
- Example: Protector-123.exe
Keep in mind that the USERNAME will be your user name The file is called protector-(random).exe Expect this name to change over time.
Once you locate the file you will need to re-name the file. To do this you can right click on the file named and select “Re-name”. Name it whatever you want. Once done re-start your computer. Next time you boot up the virus should not be running. Now you should be able to delete the file name.
At this time you should run a full virus scan. We Recommend Spyware Doctor with Antivirus. However you can use any client you trust the most. To see a list of other clients we recommend check out our Anti-virus Reviews section.
Windows Virtual Security Registry Removal Procedures
We don’t recommend that users manually edit the registry. Aside from the issue this infection causes with executable files, there shouldn’t be any damage to the registry that cannot be solved automatically by a good antivirus program and registry cleaning software. You may want to use a registry cleaner like PC Health Advisor Here to clean out the registry and scan for other malware. You can also read all or registry cleaner reviews
Windows Virtual Security Directories:
Windows 7 / Windows Vista
- %AppData%\NPSWF32.dll
- %AppData%\Protector-Random 3 to 4 characters example (acf).exe
- %AppData%\Protector-Random 3 to 4 characters example (acf).exe
- %AppData%\result.db
%AppData% refers to the current users Application Data folder. By default, this is C:\Documents and Settings\<Current User>\Application Data for Windows 2000/XP. For Windows Vista and Windows 7 it is C:\Users\<Current User>\AppData\Roaming
If you require advanced help or just want an expert to remove the virus than use this computer repair service. The charge is under a hundred bucks and they can often get started right away. These are real experts when it comes to malware and virus removal.
Related Article Keywords: Windows Virtual Security , Remove Windows Virtual Security , Windows Virtual Security Removal, How to Remove Windows Virtual Security