Web Layers is another malicious piece of software that will display unsolicited ads in your browser and redirect you to malicious websites. If you notice unusual activity on your computer caused by Web Layers, then it is recommended that you remove the software as soon as possible.
Web Layers is another piece of software installed by SuperWeb. The goal of the software is to display advertisements. SuperWebs has a reputation for releasing software of this type with past applications that include Polished Patterns and Application Nation. There is a website where the software can manually be installed, but it appears to be nonfunctioning. Therefore, most of the infections are coming from it being bundled with other software. Therefore, it is important to be careful when installing applications from third-party download sites.
Once the application is installed it will connect to its servers and start rendering ads on your computer. It most commonly uses ads in the form of popups or coupons. Many of these direct you to other malicious website which can result in even more infections.
The software will also monitor your surfing habits and send the information off for review. This can be useful for them to develop further advertisements and applications.
We have included steps below to remove Web Layers manually. It is not very difficult. However, if you would like a more automated and simple way to remove the application then we recommend SpyHunter. This free program will scan your computer and alert you to any issues it finds.
Uninstall Web Layers from Windows.
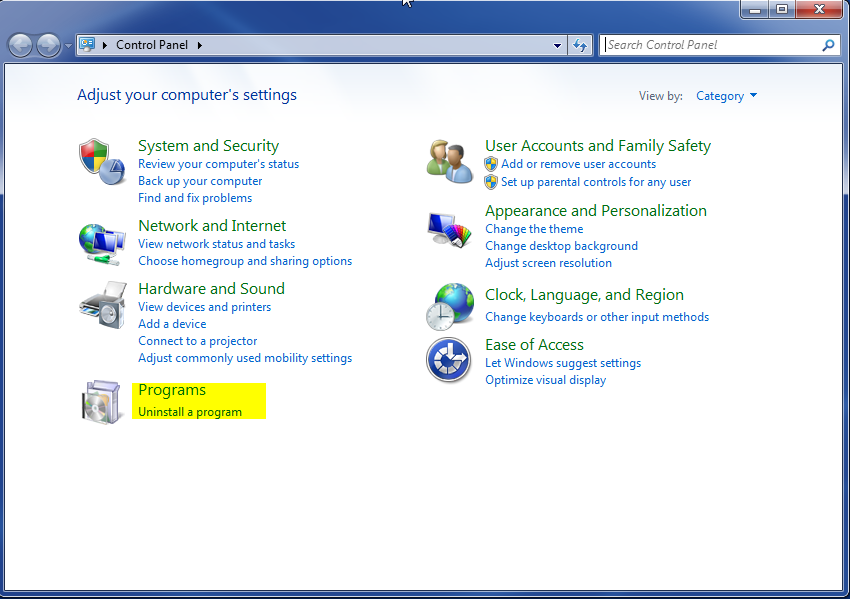
- Open up control panel by clicking on the start button in the lower left corner of your computer, and then going to Control Panel

- Once, you are in Control Panel, go to the link labeled “Uninstall a Program”. If your computer does not look like the view below, you may have to sort by categories at the top right.
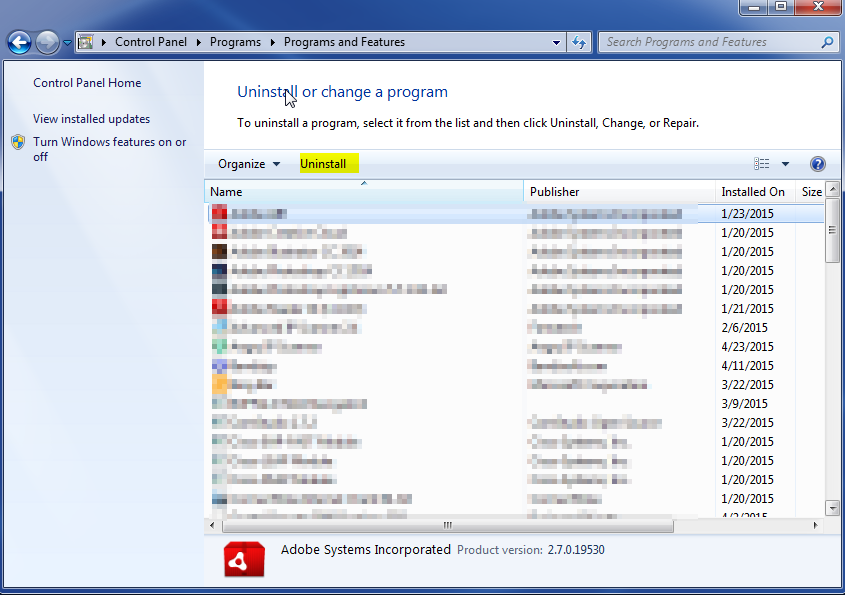
- Once in the uninstall programs section, look for the offending program. You can scroll by date installed to find programs that were installed recently. This may be a clue as to what the offending program is. Once you have found the program, highlight it and select “Uninstall” to remove
Once you have done this, you will need to go into your browser and set it to its default settings to remove the other changes it made. You will also want to scan your computer to make sure no new issues were introduced by the vulnerability. A good tool to use for this is MalwareBytes. If you already have a virus scanner, you should run this as well.