In an era dominated by the rapid advancement of technology, the importance of cybersecurity has never been more crucial. As we navigate an increasingly interconnected world, safeguarding our digital lives and protecting sensitive information has become paramount. In this blog post, we embark on a visual journey into the dynamic realm of cybersecurity, where we explore the intricate, invisible battles that take place on a daily basis. Through a captivating collection of images, we’ll not only showcase the sophisticated tools and strategies used to defend against cyber threats but also shed light on the digital landscapes where these battles are fought. Join us as we delve into the fascinating, ever-evolving field of cybersecurity, and discover the technologies and practices that are at the forefront of our digital defense.

“University of Maryland and Sourcefire Announce New Cybersecurity Partnership” by Merrill College of Journalism Press Releases is licensed under CC BY-NC 2.0 .

“New Federal Legislation and WikiLeaks Attacks Frame University of Maryland Cybersecurity Center Launch” by Merrill College of Journalism Press Releases is licensed under CC BY-NC 2.0 .

“Illinois State University President Dr. Terri Goss Kinzy speaks at the ISU Cybersecurity program open house” by State Farm is licensed under CC BY 2.0 .

“Pat Vickman, Illinois State University Vice President for University Advancement, speaks at the ISU Cybersecurity program open house” by State Farm is licensed under CC BY 2.0 .
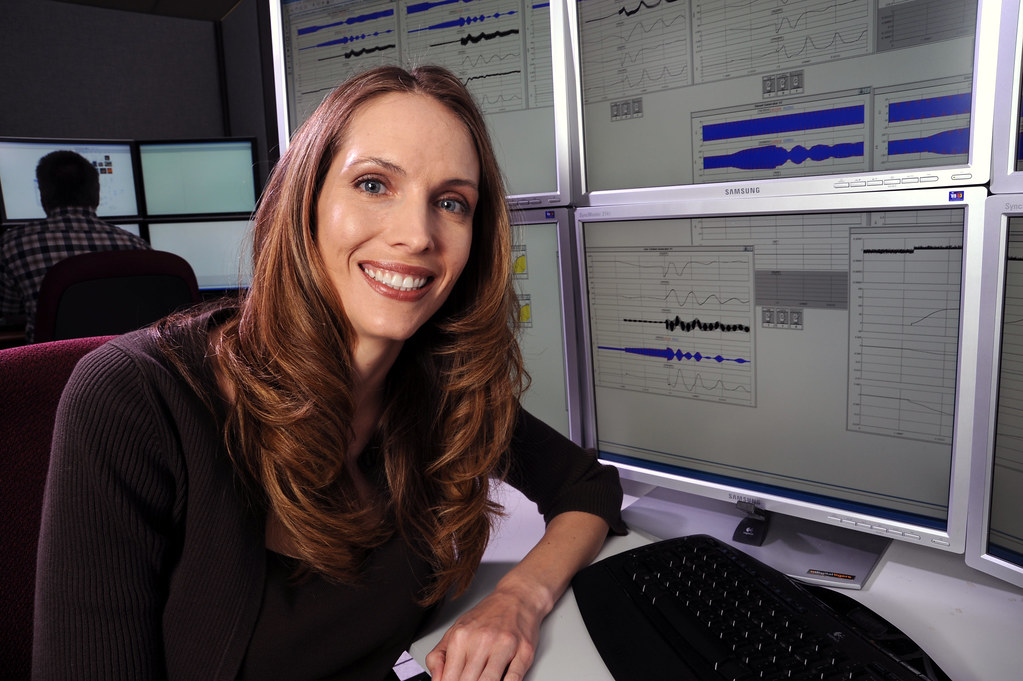
“Cybersecurity” by Idaho National Laboratory is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“Signing Ceremony for National Cybersecurity Center of Excellence” by MDGovpics is licensed under CC BY 2.0 .

“New UMD Cybersecurity Center Aims at Public-Private Partnerships” by Merrill College of Journalism Press Releases is licensed under CC BY-NC 2.0 .

“President Donald J. Trump Signs the Cybersecurity and Infrastructure Security Agency Act” by The White House is marked with Public Domain Mark 1.0 .

“Deputy Minister Pinky Kekana addresses CEO Forum for Cybersecurity” by GovernmentZA is licensed under CC BY-ND 2.0 .

“Deputy Minister Pinky Kekana addresses CEO Forum for Cybersecurity” by GovernmentZA is licensed under CC BY-ND 2.0 .

“Deputy Minister Pinky Kekana addresses CEO Forum for Cybersecurity” by GovernmentZA is licensed under CC BY-ND 2.0 .
As we conclude our exploration of the captivating world of cybersecurity, it becomes abundantly clear that the stakes in the digital realm have never been higher. The images presented throughout this blog post serve as a visual reminder of the vigilance and innovation required to protect our data, privacy, and the very foundations of our interconnected society. Cybersecurity is an ongoing battle against an invisible and ever-evolving enemy, and the visual representations of this fight illustrate the dedication of countless individuals and organizations committed to securing our digital future. As we marvel at the sophisticated technology and strategies employed in this field, we are left with a profound appreciation for the cybersecurity professionals who work tirelessly to defend against digital threats. Our journey through these images is not just a visual spectacle; it’s a powerful testament to the vital importance of cybersecurity in our increasingly digital lives, and a call to remain vigilant and informed in this ever-evolving landscape.