SupermanCoupon is a new adware program that is wreaking havoc on the Internet and on people’s computers lately. The software should be removed from your system as soon as you notice it because it provides no clear positive purpose to be on your computer.
Like many other applications it promises to be a useful tool to enhance your browsing experience. But, once again it is just a trick to get you to install the software so you can be bombarded with all manner of ads.
The program is a browser extension that can be run in all the popular browsers like Google Chrome, Mozilla Firefox and Internet Explorer. It will contact several adware servers and begin hammering you with ads you didn’t want to see. It will usually show in banner ads, popups and coupons within your browser.
Like many other adware programs, it finds its way into your system through bundled software. This is why it is important to be careful when installing applications from third-party download sites. Furthermore, never do the automated installation process. Always try to do the manual installation. This will allow you to select and remove the programs you do not want to be installed. Pay close attention to the options or you could inadvertently install something that you do not want on your system.
If you need an easy way to remove the malware from your system, we recommend SpyHunter. It is an easy, automated way to remove these types of issues from your computer.
Uninstall SupermanCoupon from Windows.
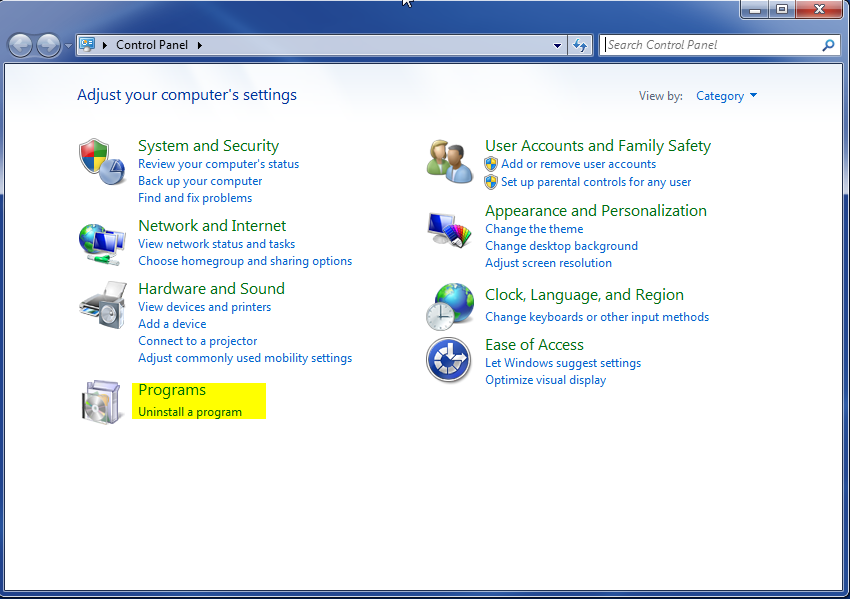
- Open up control panel by clicking on the start button in the lower left corner of your computer, and then going to Control Panel

- Once, you are in Control Panel, go to the link labeled “Uninstall a Program”. If your computer does not look like the view below, you may have to sort by categories at the top right.
- Once in the uninstall programs section, look for the offending program. You can scroll by date installed to find programs that were installed recently. This may be a clue as to what the offending program is. Once you have found the program, highlight it and select “Uninstall” to remove

Once you have done this, you will need to go into your browser and set it to its default settings to remove the other changes it made. You will also want to scan your computer to make sure no new issues were introduced by the vulnerability. A good tool to use for this is MalwareBytes. If you already have a virus scanner, you should run this as well.