The MyStart Search Protectoin program is another annoying piece of software that is meant to protect other programs it bundles with. This is to make sure they stay installed and are difficult to remove by the user. This keeps them earning money and keeps the annoyances on your computer. MyStart Search Protection will also change the home page on your computer to mystart.com and it will change your default search engine. It will also prevent you from reverting to other settings in the browser. It will block you from doing so and will show a warning in the system tray.
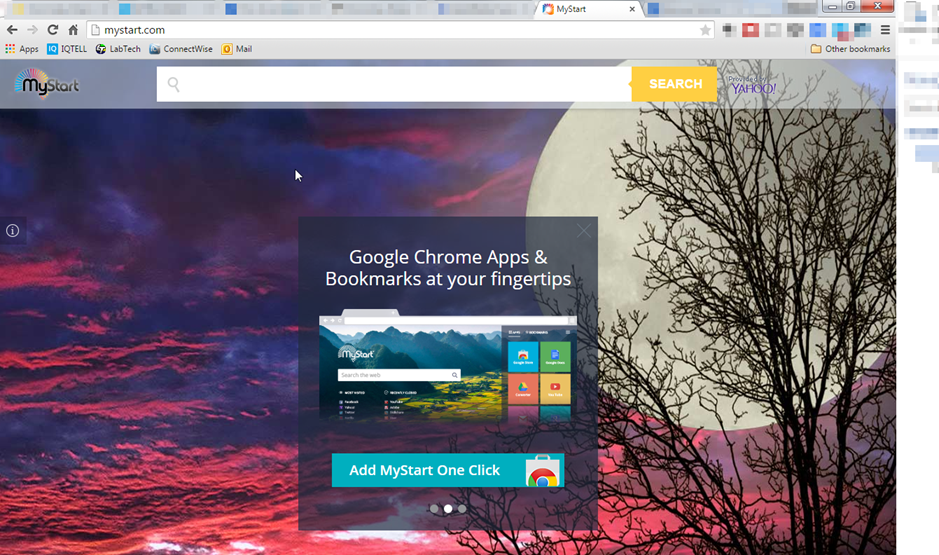
This program is developed by a software company called Spigot. They have a reputation for developing malicious software. A good clue that it is installed on your machine is if you have a process running in your computer called SearchProtection.exe. You can find this by typing CTRL+ALT+DEL and selecting TASK Manager.
If you would like an easy way to remove this malicious software, you can check out SpyHunter. This software will attempt to automatically detect and remove the offending program from your computer.
The program is typically installed when you download and run other free software. Typically, you will be alerted during the install process if you use the custom install. However, since most people do not pay attention then the software makes it onto many computers. Sometimes people have no idea how the software even made it onto their computers.
Its not technically a virus, but it does have several capabilities that should raise questions. It has rootkit abilities and can do browser hijacking. It can also be a real pain and nuisance for working with your computer. Unfortunately, the software is bundled with software downloaded from reputable download sites. Therefore, never trust downloads completely. Always try to do a custom install and pay attention to the options as you go through the wizard.
It can also be bundled with many toolbars available for download. Be very careful when installing these as well. Again, select the custom installation so you can watch what is being installed on your computer.
Uninstall MyStart Search Protection from Windows.
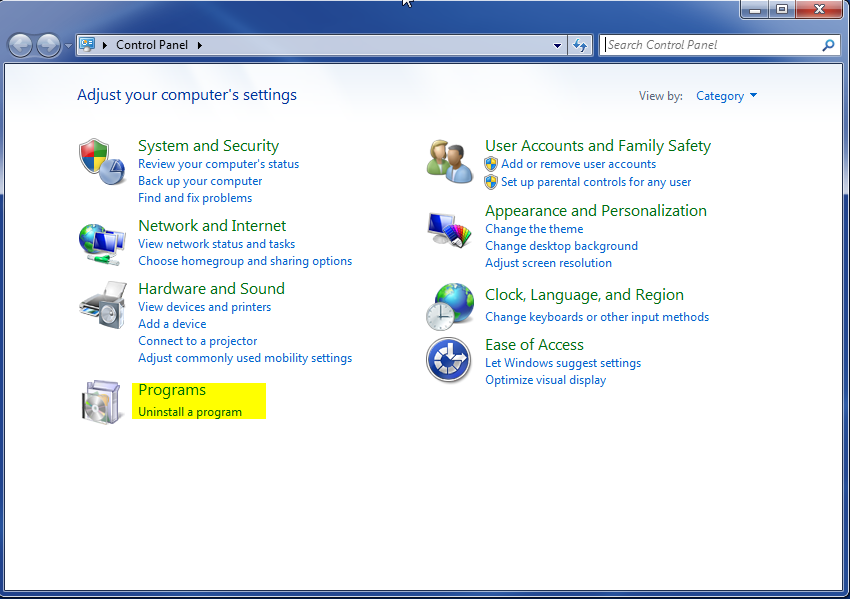
- Open up control panel by clicking on the start button in the lower left corner of your computer, and then going to Control Panel

- Once, you are in Control Panel, go to the link labeled “Uninstall a Program”. If your computer does not look like the view below, you may have to sort by categories at the top right.
- Once in the uninstall programs section, look for the offending program. You can scroll by date installed to find programs that were installed recently. This may be a clue as to what the offending program is. Once you have found the program, highlight it and select “Uninstall” to remove
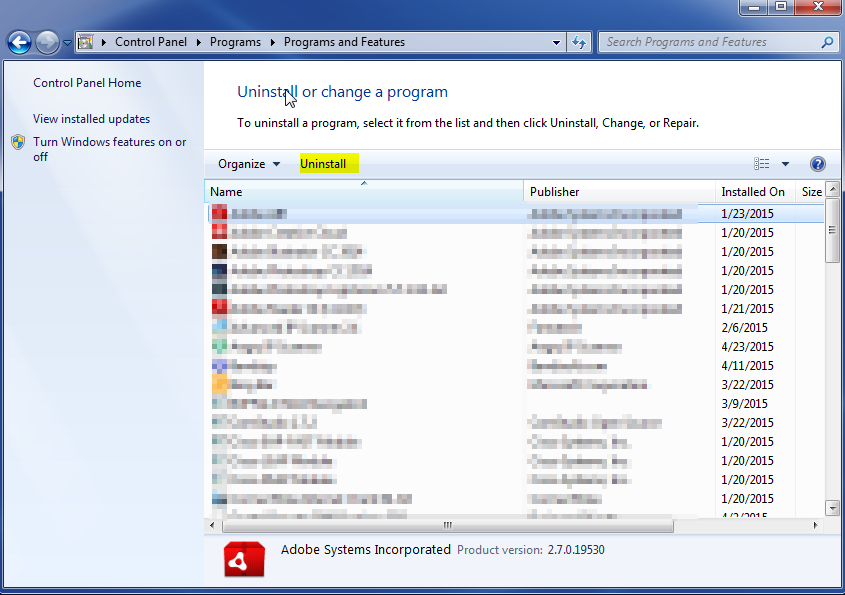
Once you have done this, you will need to go into your browser and set it to its default settings to remove the other changes it made. You will also want to scan your computer to make sure no new issues were introduced by the vulnerability. A good tool to use for this is MalwareBytes. If you already have a virus scanner, you should run this as well.