Easiest Removal Option:
Remote Repair: Paying an expert to remove this threat is always the easiest option. It’s also the most expensive. PCTechGuide.com has reviewed several remote computer repair companies and we recommend http://www.pcninja.com This is a small computer repair company (Two brick and motar stores in California ). Small companies like this tend to deliver better customer service. With a fully trained and experienced staff all based in California doing the repairs, you can’t go wrong. The cost for most virus removal services is around $99 USD.
Software Option:
Antivirus Clients: Anti-Virus software was developed to remove these exact kind of threats. Most people who get infected with malware get infected from having no protection or from using a free client that offered no real up front protection. It’s important to secure your computer so know one gains access to it and to protect your identity online.
PCTechGuide.com has reviewed hundreds of software vendors over the years. See our Antivirus Reviews and Internet security reviews for full in-depth reviews.
To Remove this virus we recommend Spyware Doctor with Antivirus or Malwarebytes. All three offer good results in most cases.
Do It Yourself Removal Guide
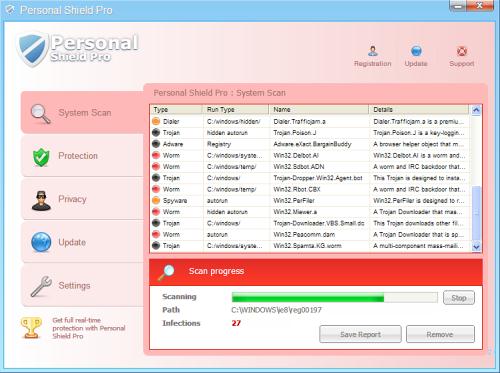
How to remove Personal Shield Pro DIY Steps
It is recommended to proceed with caution. PCTechGuide.com does not offer any warranty related to the actual results of this malware removal guide as in most cases there may be other malware software already present in your system, making the removal of Personal Shield Pro even more difficult.
Make sure that all your important data has been saved to a backup disk and that you are using genuine Personal Shield Proware in order to identify any other viruses affecting the operating system’s normal functionality.
Additioanlly, requesting technical support from a computer repair site such as http://www.pcninja.com will result in a more confortable Personal Shield Pro removal process.
Step 1. The most important step when learning how to remove Personal Shield Pro is stopping its main running process and deleting the executable from disk. Here are some methods that can be used to accomplish this objective:
A. Boot into safe mode with networking and access the Personal Shield Pro executable path. While in safe mode the malicious software will no longer be running, you will be able to effectively delete it without any problem. Below you can find the Personal Shield Pro executable paths, according to different operating systems:
XP: Personal Shield Pro executable path:
C:Documents and SettingsAll UsersApplication Data[random].exe
Win 7 / Vista: Personal Shield Pro executable path:
C:ProgramData[random].exe
It is important to note that Personal Shield Pro will in most cases have a randomly named executable file name, reason why you will have to carefully identify the correct file before deleting anything.
B. Depending on the operating system version, it may be possible to browse to the folder paths indicated above and rename the executable file associated with Personal Shield Pro to a different name of your choice. In this way, after a system reboot, Personal Shield Pro will no longer automatically start, allowing you to delete the file in question.
C. Access the above mentioned Personal Shield Pro executable path and sort the entire folder content by date modified. In this way, even if this fake antivirus software has a random executable name you will be able to rule out all other files and properly identify the one related with the rogue software. Once this is done, delete the file and restart your computer in order to stop Personal Shield Pro from execution.
D. Using the Task Manager, examine the list of running processes and identify the one related with Personal Shield Pro. Stop the process related to the fake antivirus software and delete the file in question according to the executable paths indicated in this article.
Step 2. Once Personal Shield Pro is no longe running it is recommended to delete any executable file associated with this malicious software. Act with caution and remember that the usage of legitimate antivirus software may be required in order to properly identify all files related to this rogue antivirus.
Step 3. Run an anti-virus scan as soon as possible in order to make sure that there are no auxiliary infections present in the system. We recommend the usage of one of the following legitimate security products: Spyware Doctor with Antivirus and Malwarebytes. Please note that these products are free to try and they will help you to identify any other infections that are affecting your operating system. If you feel like a manual removal is not possible (true in most cases) then we recommend that you purchase one of the above genuine antivirus products in order to protect your system from further infections.
How not to Get Infected Again
In most cases users get infected with viruses and malware from not having propper up-front protection. Computer security experts recommend that you use an anti-virus client that offers up front protection to block viruses from installing and a security client that keeps up to date with the latest virus defenitions. The paid versions of Spyware Doctor with Antivirus and Malwarebytes fit this criteria. Going with one of these clients is a step in the right direction to protecting your computer.
Need More Help? Want to Say Thanks?
Ask questions or post your comments below. Thank You.
Discalimer: PCTechGuide.com does make money from users who make a purchase of many of the products and services featured on this website.