CrossBrowser is another annoying virus that invades our computers through our online activities. It primarily prays on Chromium based browsers. Not surprisingly it is designed to deliver ads through the browser and it will alter your search results to promote advertisers.
Like many others, it bundles itself with other downloads. Typically it will sneak itself onto your computer through the installation of other applications and programs. It will come bundled with free software you get from cNet, Snapfiles and other free download sites.
You will notice banners embedded into the websites that you visit. It will also turn text in the page into hyperlinks. It will cause popups during your browsing that will further promote other fake updates and software. This can cause further installation of adware and malware.
If you would like to easily remove CrossBrowser, you can check out Spy Hunter. It will make the uninstallation and removal automated and easy.
It is important to pay careful attention when you are installing programs from free download sites. Always do the custom installation process. This will give you the opportunity to deny extra programs. If you run the default installer it will often skip the option to deny these extra programs.
While doing the custom installation, pay attention to extra installs and elect to skip them if possible.
Uninstall CrossBrowser Ads from Windows.
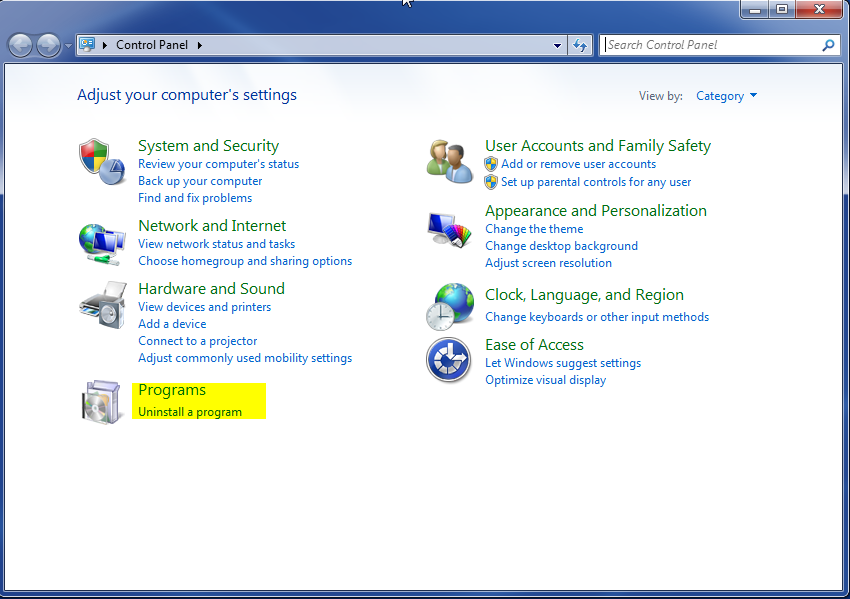
- Open up control panel by clicking on the start button in the lower left corner of your computer, and then going to Control Panel

- Once, you are in Control Panel, go to the link labeled “Uninstall a Program”. If your computer does not look like the view below, you may have to sort by categories at the top right.
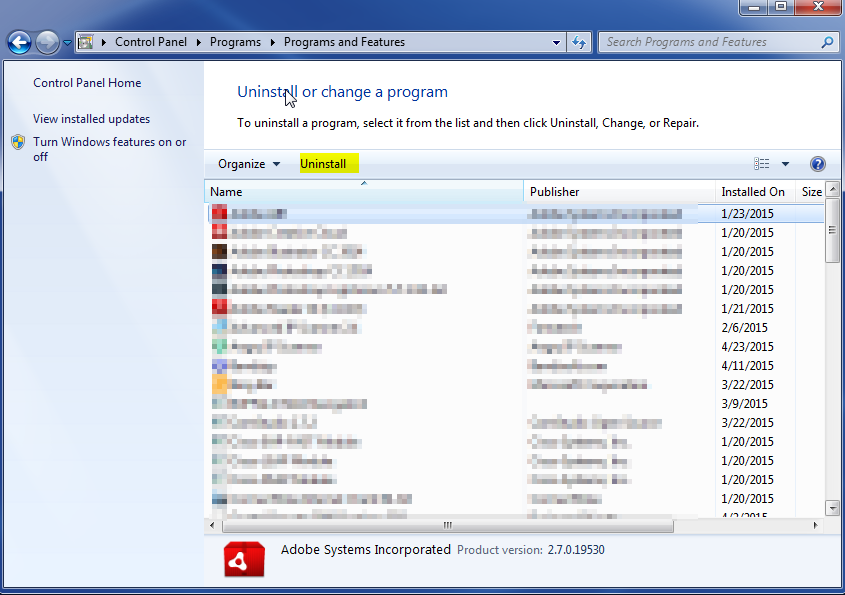
- Once in the uninstall programs section, look for the offending program. You can scroll by date installed to find programs that were installed recently. This may be a clue as to what the offending program is. Once you have found the program, highlight it and select “Uninstall” to remove
Once you have done this, you will need to go into your browser and set it to its default settings to remove the other changes it made. You will also want to scan your computer to make sure no new issues were introduced by the vulnerability. A good tool to use for this is MalwareBytes. If you already have a virus scanner, you should run this as well.